

A Wall Street Journal article last week revealed some new concerns from the Department of Homeland Security on cybersecurity in our critical infrastructure. DHS made headlines back in March when they specifically called out cyberthreats to our critical infrastructure back in March. Russia was the specific subject of this warning and here is the summary description from the March Announcement:
“Since at least March 2016, Russian government cyber actors—hereafter referred to as “threat actors”—targeted government entities and multiple U.S. critical infrastructure sectors, including the energy, nuclear, commercial facilities, water, aviation, and critical manufacturing sectors.
Analysis by DHS and FBI, [SIC] resulted in the identification of distinct indicators and behaviors related to this activity. Of note, the report Dragonfly: Western energy sector targeted by sophisticated attack group, released by Symantec on September 6, 2017, provides additional information about this ongoing campaign. [1](link is external)
This campaign comprises two distinct categories of victims: staging and intended targets. The initial victims are peripheral organizations such as trusted third-party suppliers with less secure networks, referred to as “staging targets” throughout this alert. The threat actors used the staging targets’ networks as pivot points and malware repositories when targeting their final intended victims. NCCIC and FBI judge the ultimate objective of the actors is to compromise organizational networks, also referred to as the “intended target.””
This was the first real statement from DHS directly attributing cyber-attacks on our critical infrastructure to the Russian Government. The comments made by DHS earlier this week indicate that they have learned, or are at least releasing, some important new facts about how deep these Russian-backed hacker groups have infiltrated the critical infrastructure. According to DHS officials, the Russians attacked multiple control rooms starting in 2016 and that these attacks had “hundreds of victims.”
The group responsible for these attacks, dubbed Energetic Bear/Dragonfly, is the same called out in the March DHS announcement and the Symantec report. DHS believes the campaign is most likely still going on and that many companies may not even realize they have been compromised. This not a new fight for DHS, which has been warning end users across the critical infrastructure and industrial segments for many years about the possibility of these attacks. As a much clearer picture has formed as to where these attacks are coming from and who is responsible, the alarm bells are becoming much louder. The statements made by DHS in the past six months have been much more detailed and strident than in the past several years.
So how did they get their fingers on the switch in the first place? DHS made it clear that these attacks were multi-stage attacks that usually started with phishing attacks designed to get steal users’ credentials. Most of the relationships that were exploited by the hackers were not at the utility companies themselves, but with trusted suppliers and systems integrators who have access to installed systems and equipment. These third-party suppliers don’t have to adhere to the same cybersecurity standards and regulations as the utility companies. Spear phishing and watering hole attacks were launched at these suppliers. Once the attackers got access to the supplier’s company networks, they were able to get login information for the networks at the utilities.
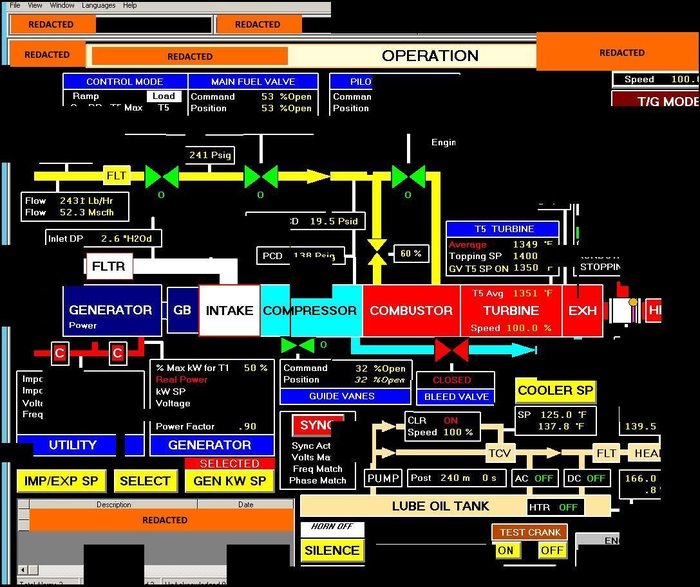
According to DHS chief of industrial control system analysis Jonathan Homer, “They got to the point where they could have thrown switches.” Michael Carpenter, former deputy assistant secretary of defense, told the WSJ “They’ve been intruding into our networks and are positioning themselves for a limited or widespread attack. Mr. Homer also expressed concerns over the Russians potentially automating their attacks.
Many in the industry have called such comments hyperbole and even hysteria. While ARC doesn’t believe that we are under an imminent threat of nationwide blackouts and we don’t advocate spreading hysteria, it is necessary to raise awareness and get end users in infrastructure and industry to pay closer attention to cybersecurity. Many end users and owner/operators are not where they need to be when it comes to good cybersecurity practice and developing a good cybersecurity organization.
The announcement in March and these recent statements should be a call to action for end users in the utilities, critical infrastructure, industrial, and smart cities sectors. DHS has been trying to develop more cooperation with the industrial and infrastructure segments. The DHS NCCIC (National Cybersecurity and Communications Integration Center) is “conducting a series of webinars on Russian government cyber activity against critical infrastructure (as detailed in NCCIC Alert TA18-074A), which will feature NCCIC subject matter experts discussing recent cybersecurity incidents, mitigation techniques, and resources that are available to help protect critical assets.”
The last webinar will be held from 1-2:30 p.m. ET on Wednesday, August 1. You can attend the session by visiting https://share.dhs.gov/nccicbriefings or dialing 1-888-221-6227. Attendees may access the webinar as a guest on the day of each event; a registered account is not required for attendees to join.

